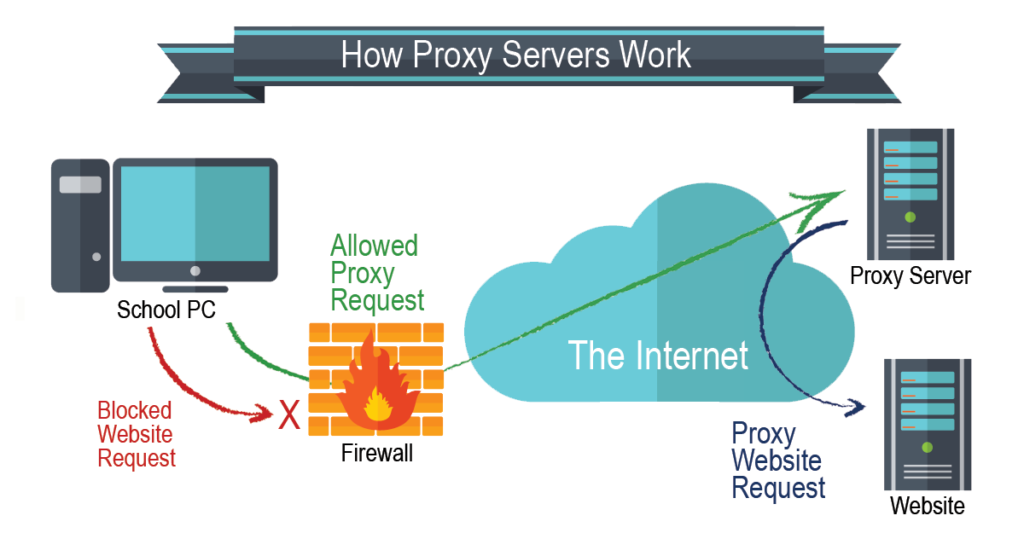
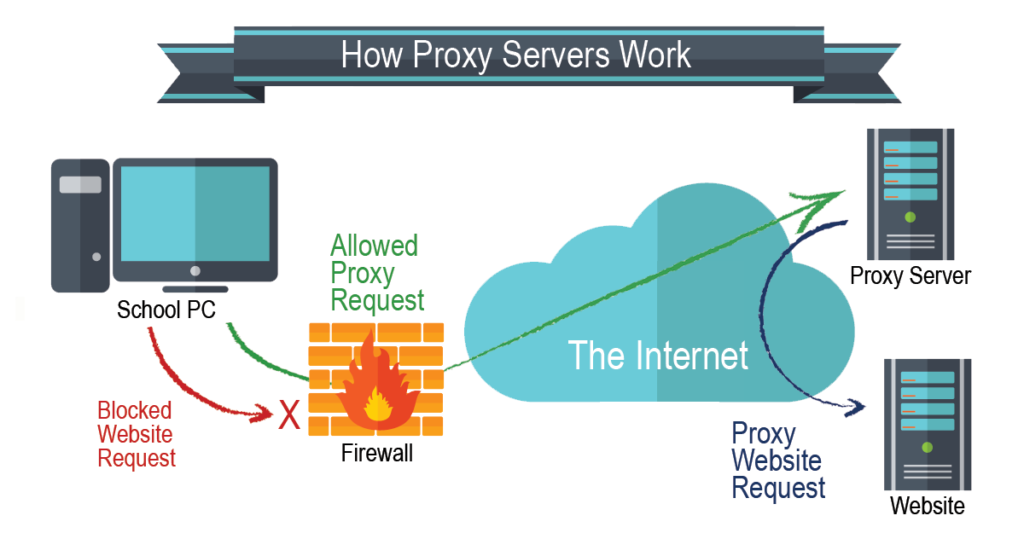
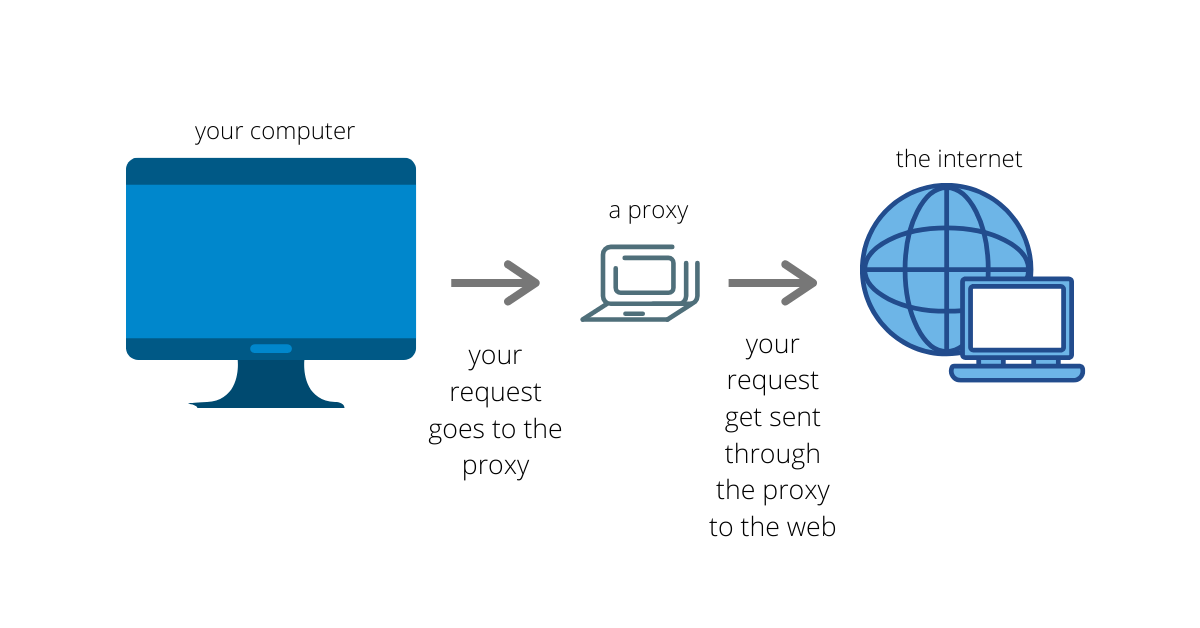
A proxy server is a server that acts as an intermediary between your computer and the internet. When you send a web request, your request goes to the proxy server first. The proxy server then makes your web request on your behalf, collects the response from the web server, and forwards you the web page data so you can see the page in your browser.
A request proxy is a type of proxy server that is specifically designed to forward web requests. Request proxies are often used to improve performance, security, and privacy.
How does a request proxy work?
When you use a request proxy, your computer is configured to send all web requests to the proxy server first. The proxy server then forwards your requests to the appropriate web servers. When the web servers respond, the proxy server forwards the responses back to your computer.
Benefits of using a request proxy
There are several benefits to using a request proxy, including:
- Improved performance: Request proxies can improve performance by caching web pages and other resources. This means that when you visit a web page that you have visited before, the proxy server can serve you the cached copy of the page, which can be much faster than downloading the page from the web server again.
- Enhanced security: Request proxies can also enhance security by filtering out malicious traffic and hiding your IP address from web servers. This can help to protect you from phishing attacks and other online threats.
- Increased privacy: Request proxies can also help to increase your privacy by hiding your browsing history from web servers. This is because the proxy server is the one that is making the requests on your behalf.
Use cases for request proxies
Request proxies can be used for a variety of purposes, including:
- Web scraping: Web scraping is the process of automatically extracting data from web pages. Request proxies can be used to avoid getting blocked by web servers when scraping large amounts of data.
- Bypassing geo-restrictions: Some websites are only available to users in certain countries. Request proxies can be used to bypass these geo-restrictions and access websites from anywhere in the world.
- Protecting your privacy: Request proxies can be used to hide your IP address from web servers, which can help to protect your privacy.
How to set up a request proxy
There are two main ways to set up a request proxy:
- Use a web proxy: There are many free and paid web proxies available online. To use a web proxy, simply configure your computer to send all web requests to the proxy server's IP address.
- Set up your own proxy server: If you need more control over your proxy server, you can set up your own. There are a number of different proxy server software packages available, both free and paid.
Once you have set up a request proxy, you can start using it to improve your performance, security, and privacy online.
Keyword silo
A keyword silo is a way of organizing your website's content around a specific topic or set of topics. This helps to improve your website's ranking in search engine results pages (SERPs) for those topics.
To create a keyword silo, you should first identify the main topics that your website covers. Then, you should group related topics together. For example, if your website is about cars, you might have the following keyword silos:
- Car models
- Car parts
- Car repairs
- Car reviews
Once you have created your keyword silos, you should optimize your website's content for the keywords in each silo. This means using the keywords in your page titles, headings, and body text. You should also create links between related pages within your website.
Creating a keyword silo is a great way to improve your website's performance in SERPs. It can also help to make your website more user-friendly, as it will be easier for visitors to find the information they are looking for.
Example of a keyword silo for the topic of "request proxy":
- Main topic: Request proxy
- Subtopics:
- What is a request proxy?
- How does a request proxy work?
- Benefits of using a request proxy
- Use cases for request proxies
- How to set up a request proxy
- Types of request proxies
- Best request proxies
- Free request proxies
- Paid request proxies
HTML format and HTML tags without , , and :
<h2>What is a request proxy?</h2> <p>A request proxy is a type of proxy server that is specifically designed to forward web requests. Request proxies are often used to improve performance, security, and privacy.</p> <h2>How does a request proxy work?</h2> <p>When WebAugust 29, 2022. In this tutorial, you'll learn how to use the Python requests library to make HTTP requests behind a proxy server. This has numerous benefits, including staying. WebIf you need to use a proxy, you can configure individual requests with the proxies argument to any request method: import requests proxies = { 'http' :. WebProxy Server Definition. A proxy server is an intermediary server separating different networks or services. What is a proxy server used for? A proxy server is used. WebRequests - Proxy. So far, we have seen clients directly connecting and talking to the server. Using proxy, the interaction happens as follows −. The client sends a request to the. WebHello world ️, In this article, I would like to show you how you can proxy HTTP requests with absolutely no coding. GIST: The idea is that we going to use API. WebProxies provide a valuable layer of security for your computer. They can be set up as web filters or firewall s, protecting your computer from internet threats like malware. This extra.
Proxy In 5 Minutes | What Is A Proxy | What Is A Proxy Server | Proxy Explained | Simplilearn

Source: Youtube.com
How To Use Proxy Servers in Python

Source: Youtube.com
What Is A Request Proxy, Proxy In 5 Minutes | What Is A Proxy | What Is A Proxy Server | Proxy Explained | Simplilearn, 7.48 MB, 05:27, 147,405, Simplilearn, 2022-01-12T15:30:06.000000Z, 2, Proxy Servers: Usage and Configuration Guide, 533 x 1024, jpg, , 3, what-is-a-request-proxy
What Is A Request Proxy.
Become Cyber Security Expert Today: taplink.cc/simplilearn_cyber_security
*Note: 1+ Years of Work Experience Recommended to Sign up for Below Programs⬇️
🔥Post Graduate Program In Cyber Security: simplilearn.com/pgp-cyber-security-certification-training-course?utm_campaign=ProxiesScribe&utm_medium=Descriptionff&utm_source=youtube
🔥IIIT Bangalore Advanced Executive Program In Cybersecurity (India Only): simplilearn.com/pgp-advanced-executive-program-in-cyber-security?utm_campaign=SCE-IIITBangaloreCS&utm_medium=DescriptionFF&utm_source=youtube
🔥Cyber Security Masters Program (Discount Code - YTBE15): simplilearn.com/cyber-security-expert-master-program-training-course?utm_campaign=SCE-MasterCS&utm_medium=DescriptionFF&utm_source=youtube
In this video on Proxy In 5 Minutes, you will understand what is a proxy?, what is a proxy server and how it works. This Simplilearn proxy explained video will help you understand the benefits of a proxy service! So, let's get started!
🔥Enroll for Free Cyber Security Course & Get Your Completion Certificate: simplilearn.com/learn-cyber-security-basics-skillup?utm_campaign=ProxiesScribe&utm_medium=Description&utm_source=youtube
✅Subscribe to our Channel to learn more about the top Technologies: bit.ly/2VT4WtH
⏩ Check out the Cyber Security training videos: bit.ly/3cMmCxj
#Proxy #WhatIsProxy #ProxyExplained #HowProxyWorks #WhatIsAProxy #WhatIsAProxyServer #Proxy #CyberSecurity #Networking #Simplilearn
✅Regarding accessibility to proxy servers, you must first set it up on your computer, device, or network. Next, check the steps required for your computer or network, as each operating system has its setup procedures. In most cases, however, setup entails using an automated configuration script.
✅There are plenty of free proxy services available on the internet. Reputed proxy providers like Smartproxy and Brightdata that run on subscription models will most likely provide credentials to log into when establishing the connection.
✅Besides allowing access to blocked content, proxies can serve as an efficient firewall system. The element of privacy proxies provides is highly lucrative to people looking to hide their actual IP address from as many prying eyes as possible.
➡️ About Post Graduate Program In Cyber Security
This Post Graduate Program in Cyber Security will help you learn comprehensive approaches to protecting your infrastructure and securing data, including risk analysis, mitigation, and compliance. You will get foundational to advanced skills through industry-leading cyber security certification courses that are part of the program.
✅ Key Features
- Simplilearn Post Graduate Certificate
- Masterclasses from MIT Faculty
- Featuring Modules from MIT SCC and EC-Council
- 8X higher interaction in live online classes conducted by industry experts
- Simplilearn's JobAssist helps you get noticed by top hiring companies
- Industry case studies in cyber security
- Access to CEH Pro Version
- 25+ hands-on projects
- Capstone project in 3 domains
- MIT CSAIL Professional Programs Community
✅ Skills Covered
- Advanced Hacking Concepts
- Network Packet Analysis
- Ethical Hacking
- IDS Firewalls and Honeypots
- Security and Risk Management
- Network Security
- Software Development Security
- Cryptography OSI and TCPIP Models
- Identity and Access Management
- Security Assessment and Testing
- Trojans Backdoors and Countermeasures
- Mobile and Web Technologies
Learn more at: simplilearn.com/pgp-cyber-security-certification-training-course?utm_campaign=ProxiesScribe&utm_medium=Description&utm_source=youtube
For more information about Simplilearn courses, visit:
- Facebook: facebook.com/Simplilearn
- Twitter: twitter.com/simplilearn
- LinkedIn: linkedin.com/company/simplilearn/
- Website: simplilearn.com
- Instagram: instagram.com/simplilearn_elearning
- Telegram Mobile: t.me/simplilearnupdates
- Telegram Desktop: web.telegram.org/#/im?p=@simplilearnupdates
Get the Simplilearn app: simpli.app.link/OlbFAhqMqgb
🎓Enhance your expertise in the below technologies to secure lucrative, high-paying job opportunities:
🟡 AI & Machine Learning - l.linklyhq.com/l/1tMt8
🟢 Cyber Security - l.linklyhq.com/l/1tMt9
🔴 Data Analytics - l.linklyhq.com/l/1tMt1
🟠 Data Science - l.linklyhq.com/l/1tMt4
🔵 Cloud Computing - l.linklyhq.com/l/1tMtA
What Is A Request Proxy, WebRequests - Proxy. So far, we have seen clients directly connecting and talking to the server. Using proxy, the interaction happens as follows −. The client sends a request to the. WebHello world ️, In this article, I would like to show you how you can proxy HTTP requests with absolutely no coding. GIST: The idea is that we going to use API. WebProxies provide a valuable layer of security for your computer. They can be set up as web filters or firewall s, protecting your computer from internet threats like malware. This extra.
Proxy Servers: Usage and Configuration Guide - Source: whatismyipaddress.com
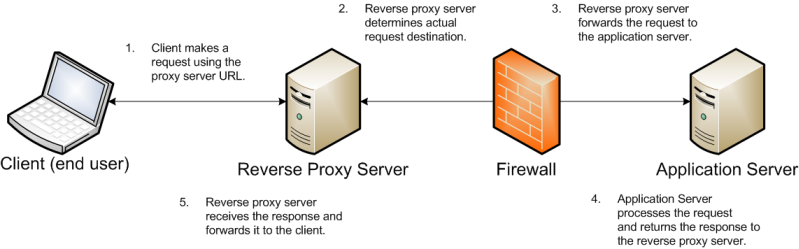
Example sequence for a reverse proxy request - Source: docs.oracle.com
What is a Proxy Server?. Have you ever been traveling and… | by Kallyas Media | Medium - Source: medium.com
Belum ada tanggapan untuk "What Is A Request Proxy"
Posting Komentar